Shadow IT Shield: A Simple Framework to Keep SMB AI Tools Safe, Verified, and Productive
Why SMBs need a simple Shadow IT Shield for AI in the winter and the new year
Winter and the start of a new year are prime times for SMBs to reset how they plan, budget, and govern technology. AI tools arrive from many corners of the organization—sometimes officially approved, often through “shadow IT” channels. When employees adopt AI tools without IT involvement, risks rise: uncontrolled data sharing, inconsistent security, hidden costs, and unpredictable outcomes. A lightweight, five-step Shadow IT Shield framework gives SMBs a practical path to discover, vet, govern, and monitor AI tools without bogging teams down in heavy governance. This approach translates risk concepts into concrete actions you can take during the winter planning cycle to keep AI tools safe, verified, and productive. By treating Shadow IT SMB AI tools as a managed portfolio rather than a wild frontier, you protect data, uphold compliance, and accelerate responsible innovation.
Step 1: Discover and inventory AI tools in use
Visibility is the foundation of governance. Start with a lightweight, accurate inventory that captures both officially sanctioned tools and shadow tools employees rely on.
- What to capture: tool name, purpose, data touched or stored, data transfer nuances, user count, department, and license status.
- How to collect: pair a quick employee survey with a low-friction asset discovery across endpoints and cloud services. Include IT, security, and department leads.
- Data flow mapping: note where data leaves your environment, who has access, and whether data transfers to third parties or consumer-grade platforms.
- Prioritization: flag high-risk tools based on data sensitivity, integration with critical systems, or lack of vendor controls.
- Quick wins: publish a living, shared inventory to a central portal and assign ownership so teams point to a single source of truth.
Frame shadow IT as a controlled risk, not chaos. Refer to it as Shadow IT SMB AI tools in conversations to emphasize shared governance over punitive action.
Step 2: Vet sources and risk
With the inventory in hand, assess each tool’s risk posture. SMBs should balance agility with safety by using a practical rubric that protects sensitive data and core operations without slowing work.
- Risk categories: data sensitivity (public, internal, confidential, regulated), data residency, access controls, and vendor security posture.
- Vendor and tool questions: who can access data, how is data stored and encrypted, what is the incident response plan, and how are sub-processors vetted?
- Compliance and governance checks: does the tool support data classification, retention policies, and audit trails? Is there a breach notification timeline?
- Exit strategy: what happens to data if the tool is decommissioned or an employee leaves? Is data portable and de-identifiable where possible?
- Simple scoring: rate each tool as Low, Medium, or High risk based on impact and likelihood. High-risk tools may require containment or removal.
Maintain a concise risk register linking each tool to an owner, risk score, and remediation plan. This makes governance practical and visible to leadership.
Step 3: Establish governance and policy
Governance should be proportional to risk and easy to operate. Create a lightweight policy that defines roles, decision rights, and the lifecycle of AI tools.
- Roles and responsibilities: IT leads policy and controls; security evaluates risk; department heads oversee team use; end users follow guidelines and report issues.
- Approval workflows: a simple, auditable process for introducing new tools or expanding usage, including quick risk checks and data handling reviews.
- Tool categorization: sanctioned, under review, and blocked. Maintain a transparent list so teams understand what’s allowed and why.
- Data governance: apply data classification, define which data can be processed by AI tools, and set retention and deletion standards.
- Policy examples: require data minimization, anonymization where possible, and credential hygiene for tools in use.
Keep the policy concise, practical, and accessible. Clear guardrails support safe experimentation and steady productivity through winter planning.
Step 4: Implement lightweight controls and approvals
Controls should reduce risk without stifling innovation. Use a pragmatic set of controls to help teams work confidently with AI.
- Default deny with an exception process: block new tool use by default, but allow scoped exceptions after a quick risk check and owner sign-off.
- Approved tools and vendors: maintain a short, vetted list. Encourage teams to start from this list before seeking new tools.
- Access controls and data handling: enforce least privilege, strong authentication, and tool-specific data handling rules. Require encryption in transit and at rest for sensitive data.
- Data provenance and audit trails: ensure tools generate logs and allow data usage tracing for accountability and incident response.
- Cost visibility: monitor AI spend, alert on unexpected charges, and tie usage to business units to avoid budget surprises in the new year.
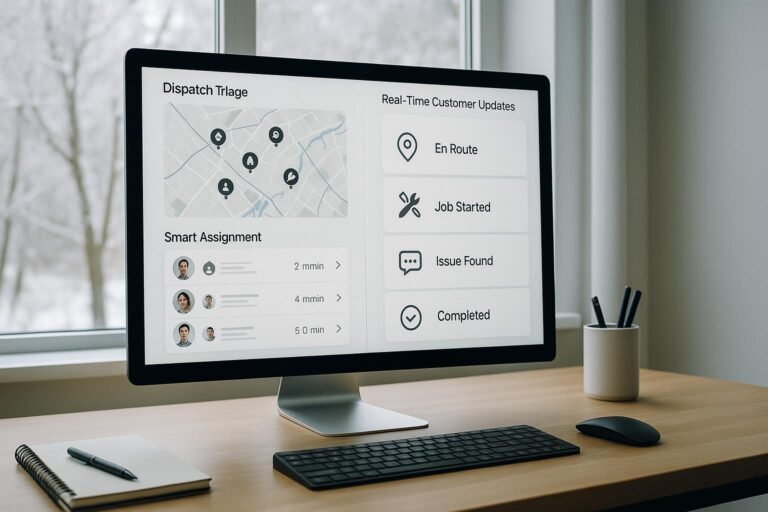
Consider a lightweight governance cockpit—a centralized dashboard for tool status, risk posture, and approvals. This Shadow IT Shield cockpit makes governance tangible and actionable during winter planning.
Step 5: Ongoing monitoring and improvement
Governance is an ongoing program, not a one-off project. Establish a cadence that fits an SMB’s resources and stays aligned with a rapidly evolving AI landscape.
- Regular reviews: quarterly or biannual checks of inventory, risk scores, and policy effectiveness. Update for new tools and changing data flows.
- Usage analytics: track tool usage by users and purpose; flag outliers or spikes that warrant a risk check.
- Incident response readiness: tabletop exercises focused on AI tool incidents and data exposure scenarios.
- Training and awareness: short, practical training on data privacy, security basics, and responsible AI adoption.
- Continuous improvement: incorporate feedback to refine inventory methods, risk criteria, and governance thresholds. Treat winter planning as a living process.
As monitoring matures, the Shadow IT Shield strengthens: fewer surprises, faster remediation, and a clear path to safe AI experimentation that supports sustainable SMB growth.